SOC 2 vs ISO 27001 for startups and mid-size SaaS
US buyers want SOC 2. European buyers want ISO 27001. The overlap between both frameworks is significant, but the way they work, what they cost, and which one you should chase first depends on who you are selling to and where your company sits right now.
US buyers want SOC 2. European buyers want ISO 27001. That’s the starting point for every compliance decision at a SaaS company.
It sounds simple. It isn’t. The two frameworks look similar on paper. Both deal with information security controls. Both require audits. Both give your sales team something to wave at procurement departments. But the mechanics are different. The costs are different. The way buyers interpret them is different. And if you pick wrong, you’ll spend months and significant money on a credential that doesn’t unlock the deals you actually need.
At Tallyfy, we went through this decision and landed on SOC 2 Type 2 first. Not because it’s objectively better. Because our buyers were primarily US-based enterprise companies, and that’s what their vendor risk questionnaires asked for. The reasoning was that simple.
But the reasoning should be that simple for you too. Let me walk through what actually matters.
The geographic split that drives everything
SOC 2 was created by the AICPA (American Institute of Certified Public Accountants). It’s a US standard, governed by a US professional body, audited by US-licensed CPA firms. When an American enterprise buyer sends you a vendor risk questionnaire, the checkbox says SOC 2.
ISO 27001 was developed by the International Organization for Standardization. It’s recognized globally. When a European buyer evaluates your security posture, they look for ISO 27001 certification. Same goes for buyers in Asia, the Middle East, Australia, and most of Latin America. The international recognition is just baked in.
This isn’t about which framework is technically superior. It’s about which framework your customer’s procurement team recognizes and trusts.
A US SaaS company selling exclusively to US enterprise? SOC 2 is the clear first move. A SaaS company based in Germany selling across the EU? ISO 27001. A US SaaS company expanding into European markets? You’re probably going to need both eventually, and the order depends on where revenue is coming from right now.
There’s a subtlety here that matters. Some US enterprise buyers will accept ISO 27001 as equivalent to SOC 2. Some won’t. The reverse is also true in Europe. But “some will accept it” is not the same as “procurement will stop asking questions.” If you don’t have the specific credential they expect, you create friction. Friction slows deals. Slow deals lose to competitors who already have the right checkbox filled.
The GDPR effect is worth mentioning. European data protection regulation has made ISO 27001 even more relevant for companies handling EU personal data. It doesn’t guarantee GDPR compliance on its own, but it demonstrates the kind of systematic approach to data protection that regulators want to see. A practical ISO guide from ISO themselves spells out how SMEs can approach this without enterprise-level resources.
How each framework actually works
The structural differences between SOC 2 and ISO 27001 matter more than most comparison articles let on.
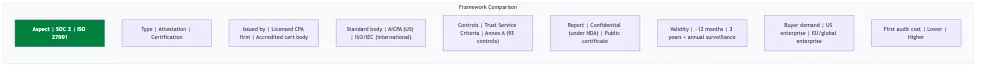 Framework comparison at a glance
Framework comparison at a glance
SOC 2 is an attestation, not a certification. A licensed CPA firm examines your controls, tests whether they operate effectively over a period of time (for Type 2), and issues a report expressing their opinion. That opinion can be unqualified (clean), qualified (issues found but not severe), or adverse (significant problems). The report itself is confidential. You share it under NDA with prospects and customers. There’s no public database of SOC 2 compliant organizations.
SOC 2 uses five Trust Service Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Security is mandatory. The other four are optional. You pick which criteria to include based on your business and what your customers care about. Most SaaS companies include Security and Availability at minimum.
The controls themselves are flexible. The AICPA doesn’t hand you a checklist of 93 specific things to implement. Instead, it defines criteria, and you design controls that satisfy those criteria for your specific environment. Your auditor then tests whether those controls actually work.
Here’s what a control mapping looks like in practice. At Tallyfy, we track controls in YAML files inside a Git repository:
- id: administrator-access
name: Administrator Access
soc2_criteria:
- CC.6.2 # Prior to issuing credentials...
- CC.6.3 # Access to information...Each control maps to specific Common Criteria (CC) references. The auditor evaluates whether your implementation of “administrator access” actually satisfies what CC.6.2 and CC.6.3 require.
ISO 27001 works differently. It’s a formal certification, not an attestation. An accredited certification body audits your organization against the standard. Accreditation bodies like UKAS (United Kingdom), ANAB (United States), or DAkkS (Germany) oversee these certification bodies to ensure quality and impartiality. You either meet the requirements and receive a certificate, or you don’t. The certificate is public. You can display it on your website, in proposals, in marketing materials.
ISO 27001 requires you to build and maintain a formal Information Security Management System, which the standard calls an ISMS. This isn’t just a collection of controls. The ISMS documentation requirements include a scope statement, information security policy, risk assessment methodology, risk treatment plan, Statement of Applicability, and evidence of management review and continuous improvement. It’s a management system with defined governance.
The 2022 revision of ISO 27001 reorganized the control structure into 93 controls across four themes: Organizational (37 controls), People (8 controls), Physical (14 controls), and Technological (34 controls). These are numbered A.5 through A.8. Where SOC 2 lets you define your own controls to meet criteria, ISO 27001 gives you a specific list and asks you to address every one. You can exclude controls that genuinely don’t apply, but you need to justify each exclusion in the Statement of Applicability.
If you want to think about how the numbering differs: SOC 2 uses references like CC.6.2 and CC.6.3 for access controls. ISO 27001 uses Annex A references like A.5.15 (Access Control) and A.8.2 (Privileged Access Rights). Different numbering systems. Similar intent behind the control.
Where the overlap helps you
Here’s the good news. If you’ve done one framework properly, a significant chunk of the work for the second is already done.
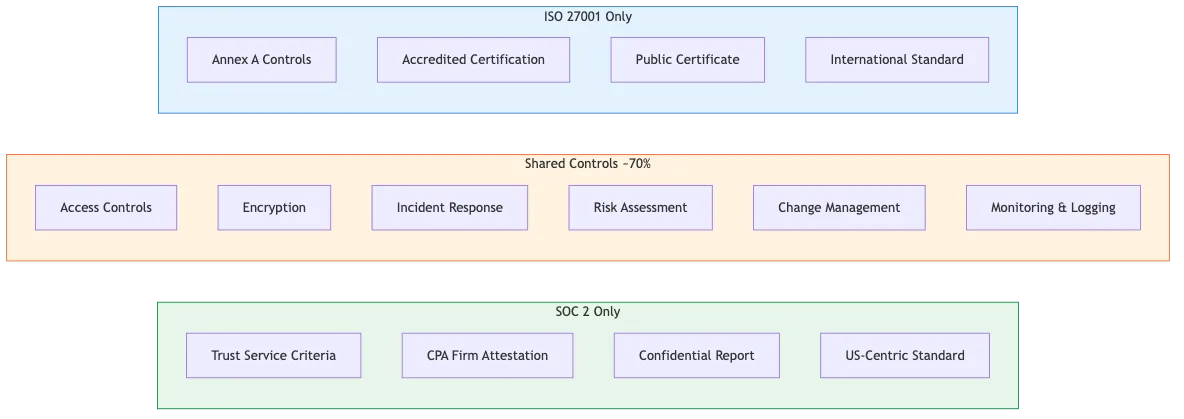 SOC 2 and ISO 27001 share roughly 70% of control requirements
SOC 2 and ISO 27001 share roughly 70% of control requirements
The AICPA published a mapping spreadsheet showing the overlap between SOC 2 Trust Service Criteria and ISO 27001 Annex A controls. The overlap sits somewhere around 80% at the control level, though real-world estimates range from 60% to 80% depending on which Trust Service Criteria you include in your SOC 2 scope and how broadly you interpret “overlap.”
This makes intuitive sense. Both frameworks care about access control. Both require incident response. Both want documented policies. Both expect vendor management. Both demand evidence of monitoring and logging. The fundamentals of information security don’t change just because one framework uses American English and the other uses international standards body language.
If you’re planning to manage compliance without expensive platforms (which I’d recommend), the overlap becomes a practical advantage. Structure your controls to map to both frameworks from the start. A single access control policy can satisfy SOC 2 CC.6.1 through CC.6.3 and ISO 27001 A.5.15 through A.5.18. You document it once. You collect evidence once. Two frameworks check the same box.
Where they don’t overlap tells you something too. SOC 2’s Availability and Processing Integrity criteria don’t have direct ISO 27001 equivalents. ISO 27001’s emphasis on ISMS governance, management review, and continuous improvement cycles goes deeper than SOC 2’s requirements. If you’re thinking about how SOC 2 intersects with other frameworks like HIPAA, the pattern is similar. Lots of shared ground, meaningful differences at the edges.
The practical implication: organizations pursuing both typically report that the second framework takes roughly 40% less effort than the first. Not free. Not trivial. But significantly less painful than starting from scratch.
The real cost and effort comparison
Let me be direct about effort, even though specific dollar amounts change constantly.
SOC 2 Type 2 is generally faster to achieve for a US-based SaaS company. If you want to understand SOC 2 basics more deeply, start there, but here’s the summary. You need to define your controls, implement them, operate them for a minimum observation period (typically six to twelve months for Type 2), and then bring in a CPA firm to audit. The audit itself takes weeks, not months. Total timeline from “we’ve decided to do this” to “report in hand” is usually twelve to eighteen months, with six to ten of those months being the observation period.
ISO 27001 takes longer upfront. Building the ISMS documentation alone takes months. You need the risk assessment, the risk treatment plan, the Statement of Applicability, the policies, the procedures, the evidence of management commitment. Then you need a Stage 1 audit (documentation review) followed by a Stage 2 audit (implementation verification). Total timeline is commonly twelve to twenty-four months.
But ISO 27001 has a cost advantage over time that people miss. The certificate is valid for three years. Annual surveillance audits during that period are typically a fraction of the initial certification cost. SOC 2 requires a full Type 2 audit every twelve months. Over a three-year cycle, the annualized cost of maintaining ISO 27001 can be comparable to or lower than maintaining SOC 2, especially for mid-size companies.
The hidden cost in both frameworks isn’t the audit. It’s the people. Someone has to own this. Someone has to collect evidence. Someone has to keep policies current. Someone has to respond when the auditor asks for documentation. At a 50-person SaaS company, this usually means one person spending 20-30% of their time on compliance activities, plus periodic involvement from engineering, HR, and leadership.
Where companies waste money: paying for expensive compliance automation platforms when a Git repository and some scripts will do the same job. I’ve written about this in detail. The audit itself requires a CPA firm (SOC 2) or accredited certification body (ISO 27001). Everything else is organization. If you want to explore that angle, talk to me about it.
Which one first and why it matters
Start with whichever one your current customers are asking for. That’s it. That’s the decision framework.
If you’re a US SaaS company with mostly US enterprise customers, start with SOC 2 Type 2. It’s what procurement expects. It’s what vendor risk questionnaires reference. It’s what your sales team needs to close deals that are stalling in security review.
If you’re selling into European markets or your customer base is international, start with ISO 27001. The global recognition removes friction across multiple geographies simultaneously.
If you’re genuinely split (say, 50% US revenue and 50% European), I’d still suggest SOC 2 first for a US-based company. The reasoning: SOC 2’s flexible control structure lets you design controls that also satisfy ISO 27001 requirements from day one. You can architect your control environment with both frameworks in mind, get SOC 2 done in twelve to eighteen months, and then pursue ISO 27001 with much of the heavy lifting already complete.
Three things to get right regardless of which you pick first.
Structure your controls to map to both frameworks from the beginning. Don’t design SOC 2 controls in isolation and then try to retrofit them for ISO 27001 later. Add both mapping references to each control from the start. It costs nothing extra during implementation and saves significant rework later.
Document everything in portable formats. We use YAML and Markdown in a Git repository. Not a proprietary platform. When your auditors change, when your certification body changes, when you add the second framework, all your documentation moves with you without migration headaches.
Collect evidence continuously, not in a panic before the audit. Quarterly evidence collection cycles with automated reminders keep the workload manageable. Annual scrambles before audit season are miserable, expensive, and produce lower-quality evidence.
The companies that handle compliance well don’t treat it as a checkbox exercise. They build it into operations. They track controls the same way they track features. They review policies the same way they review code. They collect evidence the same way they collect metrics. It becomes part of how the company runs, not something bolted on when a customer asks for it.
SOC 2 and ISO 27001 are both means to an end. The end is demonstrating to customers that you take their data seriously and you can prove it. Pick the framework that matches your market. Do the work properly. Then add the second one when the business requires it. The overlap makes the second one significantly easier than the first. That’s the whole strategy.
About the Author
Amit Kothari is an experienced consultant, advisor, coach, and educator specializing in AI and operations for executives and their companies. With 25+ years of experience and as the founder of Tallyfy (raised $3.6m), he helps mid-size companies identify, plan, and implement practical AI solutions that actually work. Originally British and now based in St. Louis, MO, Amit combines deep technical expertise with real-world business understanding.
Disclaimer: The content in this article represents personal opinions based on extensive research and practical experience. While every effort has been made to ensure accuracy through data analysis and source verification, this should not be considered professional advice. Always consult with qualified professionals for decisions specific to your situation.